The Valley processes information for its customers on a daily basis. As a professional partner and service provider, both our employees and management are very aware of the responsibilities and risks associated with processing personal data. We take responsibility in treating this information confidentially. We want to be able to guarantee a high level of security so we can be a trusted partner for our clients. The risks are periodically assessed, and appropriate measures are placed wherever needed.
Data privacy & protection

ISO certified
These risks are recorded in our procedures and processes that are guaranteed and tested against the ISO 9001:2015 (Quality) and ISO/IEC 27001:2017 (Information Security) standards. All these standards are tested annually by means of both internal and external audits. Certificates and reports of this are present and available for inspection on request. The Valley has been ISO certified since 2008, so we can rightly say that it is anchored in our DNA.
Checks and balances
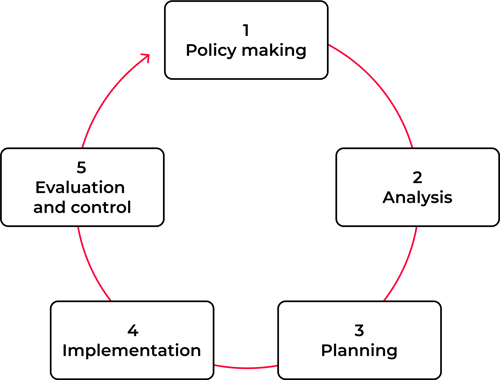
In accordance with ISO 9001 and 27001 standards, The Valley continuously focuses on improvement by using the following process:
The purpose of using the information system is to determine and lay down the objectives and principles regarding information security within The Valley. Information management is part of the quality management that is used and focuses on the following three aspects of information provision:
- Availability → information must be available at the desired times;
- Integrity → information must be correct and complete and the information systems must store and process correct and complete information;
- Confidentiality → the information should only be accessible to those who are authorized to do so.
Privacy by design
During the design phase, The Valley pays attention to privacy by design when developing a product or service (such as information systems). We adhere to the following 7 basic principles
Proactive and preventive
the design anticipates infringements and ways of dealing with them
Design
Privacy is an essential element of the core product functionality, not an afterthought
End-to-end lifecycle protection
during the entire lifecycle in the product, personal data must be optimally protected
Respect for user privacy
the interests of the data subject (client, patient and employee) must come first
Default
The default setting should adequately protect the privacy of data subjects, without users having to put in extra effort
Full functionality
In the final product, all relevant interests (including privacy) must come together instead of being crossed out – you don't have to exchange privacy for functionality
Transparent
it must be clear to customers and those involved which processing takes place